Humans have fought each other over various things and reasons from time immemorial. While some are simple to understand, some are useless and irrelevant, and some are important and necessary. There is a popular saying that there are usually no winners during wars because it is usually a no victor, no vanquish endeavour. However, this hasn’t deterred humans from trying to annihilate one another in the name of war. The Russia-Ukraine conflict (and the resultant cyberwar) happening in 2022 is proof that chaos is the natural order.
Wars are devastating; minors, women, the elderly, and livelihoods are collateral damages during these arduous events. While the United Nations (UN) charter on war states that women, children, and the elderly are to be spared in times of war, data from conflicts and war zones have shown that this is usually not the case and that no one is safe during modern-day wars.
During wars, many arsenals and tactics are deployed by those involved and obviously, the objective is to win through any means necessary. In the 21st century, the internet has become an integral part of our existence as humans, and the benefits we derive from it is enormous, no doubt. It is as essential as our ability to breathe, eat, sleep and entertain ourselves. And there is hardly any sphere of our lives that the internet isn’t used. From health-tech, self-driving cars, and space travel, the importance of the internet in our world is vast and cannot be overemphasized.
However, I have a personal theory that I think many people will tend to agree with “If it has benefits and can be used for good, it can also be used in a bad way”. As important as the internet is and with all the benefits we enjoy while using it to power this or run that; unfortunately, it can also be used to harm us either individually or collectively.
These days cyberspace has been increasingly viewed as an area of power tussle. Power contests and the quest for dominance has made cyberwarfare a fun game among the world powers. When we talk about cyber-attack, many internet users might think or assume it is just Facebook, WhatsApp, Instagram, or Twitter failing to load. Cyber-warfare goes way beyond the internet disruption of some of our social networks or apps.
Today the world runs on technology, and millions of algorithms susceptible to being hacked power these technologies. We rely on these networks and connectivity to power a lot of the things we use today, and the growing Internet of Things is incredible, but it comes with a dark side; the damage and disruption this can cause are way too much to begin to imagine.
What is a cyberwar?
Let’s begin with an excerpt from Jeremy Rabkin and John Yoo’s “Striking Power” :
The internet became accessible to general home use in 1993. That same year, an article appeared warning that future wars would turn on mastery of the cyber domain. Strategists launched the idea of “cyberwar” almost simultaneously with the emergence of the internet.
Jeremy Rabkin & John Yoo
Striking Power: How Cyber, Robots, and Space Weapons Change the Rules for War
Cyberwar or cyberattack is a broad and complex topic to define depending on the attack’s scale, size, and medium. For this article, I will limit my definitions to the confines of the ongoing conflict between Russia and Ukraine and how it has been and can be used by either side.
Cyberwarfare is a means, tactic, and tool to achieve success by inflicting maximum collateral damage on your opponent. Because it happens over the internet and computer, there are several advantages of waging war in cyberspace.
Why Countries choose cyberwarfare
- You don’t need to cover a vast distance with troops and foot soldiers or travel over a long distance to inflict the damage you intended, and everything is always within your grasp by just hacking and typing some destructive codes command.
- You can hack into your opponent’s data and steal their data, create deepfake images and spread them all over the internet as authentic images, and use this to induce fear, cyberbullying, or fear that can cripple the nation.
- You can attempt to inflict physical damage or demoralize your enemy with false news and propaganda, which are some of the tactics Putin has used to keep his people in check so far.
A real-life scenario
You can also destroy things or damage things beyond repair; for example, In November 2011, an event occurred in the normally peaceful location of Springfield, Illinois, which soon caused a considerable stir in the world’s media. The story was triggered by a pump failure at a public water plant, which caused several homes in the Springfield area to find themselves without mains water. On investigation, the pump was found to have had a fault in which it had been turning itself off and on inexplicably, eventually failing.
Analysis of the fault traced the problem back to five months previously. It was discovered that there was consistent traffic between a Russian internet protocol (IP) address and the Illinois plant’s Supervisory Control and Data Acquisition (SCADA) system –– essentially the plant’s control network, which can be accessed in certain circumstances over the internet to effect remote controls. The fault in the pump seemed to have developed after this initially unidentified connection over the internet from Russia.
Unlike the UN charter on nuclear weapons with a set of ground rules to follow, there are no rules for waging and conducting cyberwarfare; everything and anything connected to the internet is vulnerable.
In late November 2014, Sony Pictures Entertainment was hacked by a group calling itself the Guardians of Peace. The hackers, widely believed to be working in at least some capacity with North Korea, stole huge amounts of information off Sony’s network. They leaked the information to journalists, who wrote about embarrassing things Sony employees had said to each other. This tells you that everything is vulnerable to hacking; even big corporations that spend millions of dollars on cybersecurity and cyber defence strategy are susceptible to massive breaches from cyber marauders called hackers.
The Cyberattacks so far
So far, the Ukrainians seem to be wreaking havoc on many Russian corporations and government establishments through a series of cyber-attacks and propaganda. There is no doubt that Ukraine has some of the world’s most prolific hackers who have now turned their attention to creating cyberattacks against Russia. Last week, they organized a crowdsourced cyber army, claiming to have knocked Russia’s biggest bank (Sberbank) off the internet. This week, the Ukrainians are taking it further by creating something for smartphones. They’re distributing an app that’s essentially an air-raid siren to warn Ukrainians of Russian attacks from the sky.

Alex Bornyakov, a former ad-tech entrepreneur, told Forbes that the army of hackers was crowdsourced through Telegram, and they aim to counter the Russian propaganda.
Our goal is to show them that politics and the way that Putin thinks and his actions are going to bring down the whole of Russia. We fight lies and fakes with transparency.”
Anonymous also hacked and leaked data belonging to the Russian Defense Ministry; the leaks contain a database of Russian military officials’ phone numbers, emails, and passwords. Many of the hacked emails end in ‘mil.ru’ or ‘gov.ru’, meaning they can only belong to the Russian military or government. The leaked data was posted on Twitter on the anonymous handle (@YourAnonTV) before it was flagged and deleted by Twitter for breaking its community guidelines.
The WSJ reported that the websites of the Russian Foreign Ministry, as well as the country’s largest stock exchange and a key state-owned bank, were hacked.
On the flip side, the notorious cybercriminal group CONTI has released a message in support of the Russian government. CONTI was behind the ransomware attack that crippled Ireland’s healthcare systems in 2021.
On their dark web blog, CONTI releases a statement saying they are
Announcing full support of the Russian government. If anybody will decide to organize a cyberattack or any war activities against Russia, we’re going to use all possible resources to strike back at the critical infrastructure of an enemy.
Aside from this statement, Russia has not launched any cyberattack on Ukraine so far. The rest of the cyber security world is closely watching and on high alert, as reported by The Economist.
The US Cybersecurity and Infrastructure Security Agency (CISA) is worried and concerned about three (3) classes of cyber-attacks or threats in the US, which I also think other countries should be concerned about on their own, and they are:
- Massive theft of intellectual property from American Corporations that could degrade or hinder economic competitiveness for generations.
- Cyberattacks that could cause massive disruptions on the American way of life, in ways that could have a devastating effect on the country.
- Cyberattacks that could degrade, disable or destroy US’ military ability to defend itself.
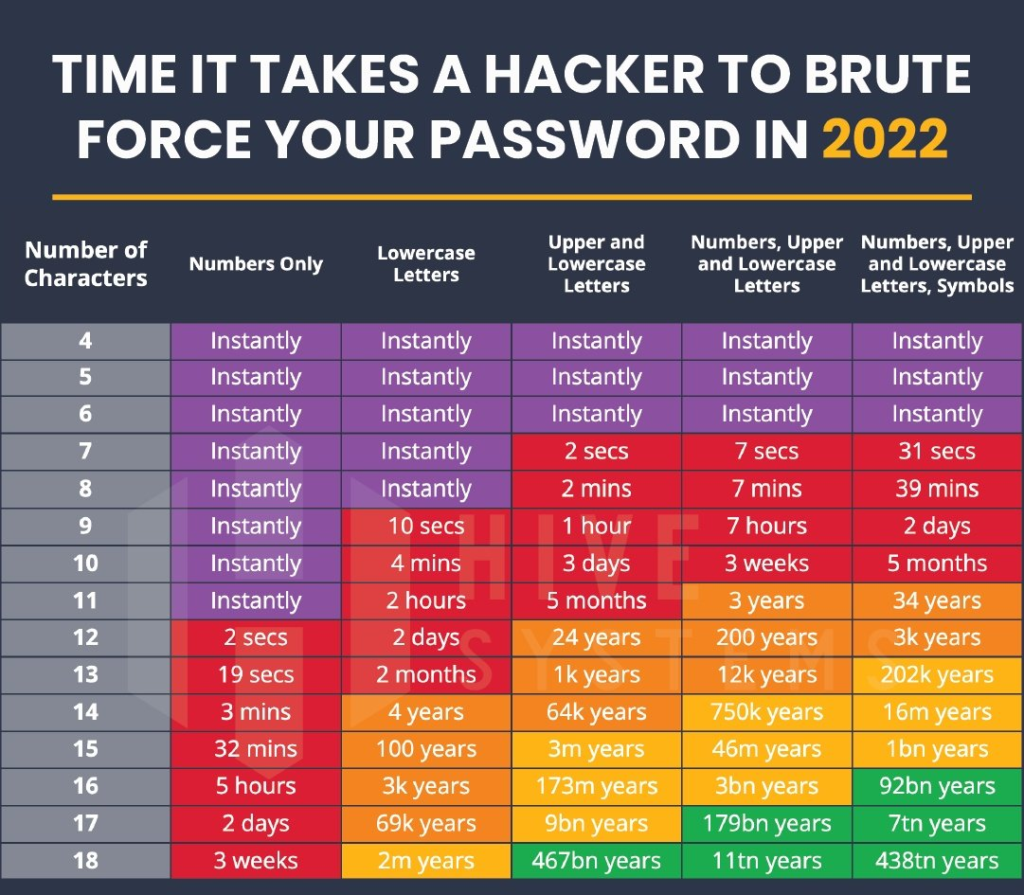
In another unrelated development to the war, according to The Verge, Samsung has confirmed that hackers have stolen the galaxy phone source code. While this may be unrelated at the moment, I strongly would urge anyone on the internet to take measures that would secure their data on the internet.
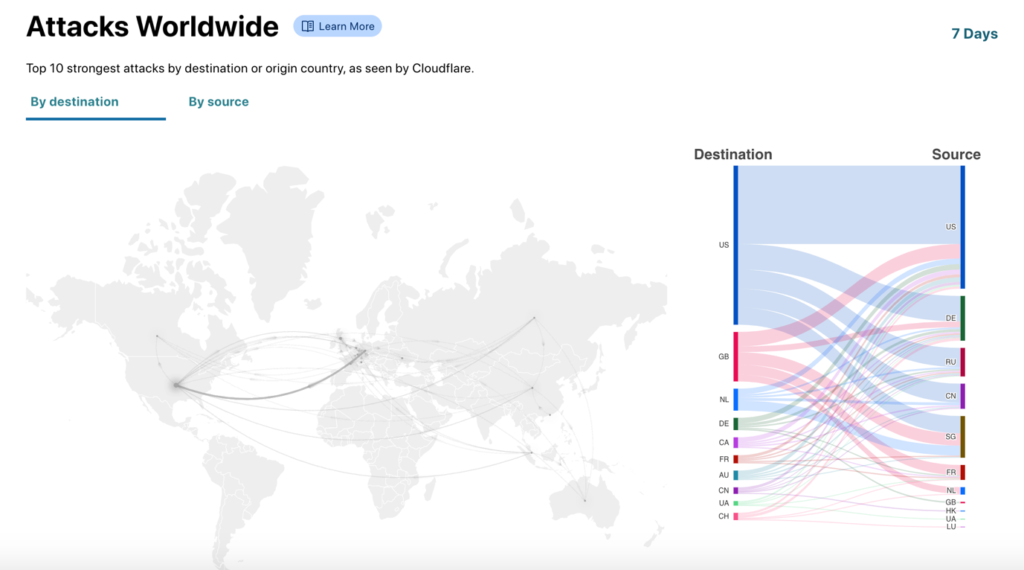
Even for the US, the cyber threat environment today is crowded, it’s complicated and uncertain, and it’s changing at the speed of the internet. So far, in the conflict between Russia and Ukraine, there have been reports of cyberattacks on both ends. This could spread to other parts of the world if caution is not taken because of the internet’s inter-connectivity and the western world’s punitive measures against the invasion. Russia could also take advantage of the situation to launch cyberattacks on countries providing support to Ukraine. Cyber security analysts believe that the art of modern warfare using cyber-attacks is more catastrophic and less expensive than using tanks and ammunitions.
On a final note, it would be best if you take proactive measures to deal with any new cyber threats that could become more prominent in this time of unprovoked war. Do not open or click any untrusted links and websites.





Add a comment